差不多我用到的大部分代碼都是從上面cv(Ctrl+c---->Ctrl+v)下來的
1、首先解決The context is partially valid. Only x86 user-mode context is available.
具體方式是hookKdpTrap
2、 防止安全組件加載失敗
SharedUserData->KdDebuggerEnabled = FALSE; //防止安全組件加載失敗,SharedUserData這個是一個導出的全局變量直接寫就行
3、XP會清零KdDebuggerEnabled
這里本來是打算做一個定時器,但是還是會導致TesNginx.Sycccccccccccccc出現藍屏,所以只有手動的去修改
4、斷鏈隱藏 kdcom,防止kdcom內存被清空導致和windbg通訊不了
5、XP會檢測KdEnteredDebugger,如果是1就直接藍屏
處理方式是讓他去找其他位置(PUCHAR)KdEnteredDebugger + 0x30; //據暗中觀察,+0x30 的位置恒為0
做完這些之后基本上就能夠下斷點了,但是其實還是有問題(由于hook了系統函數有一定的幾率會觸發109錯誤->PathGuard,一開始我也分不清楚,后來慢慢的也了解了)
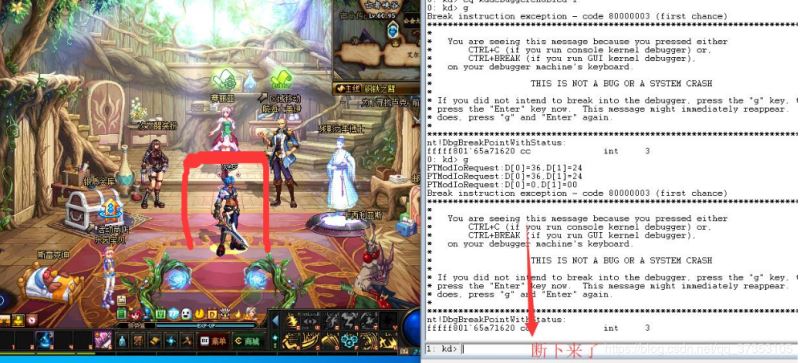
之后放上一張過了圖片
最后把代碼也帶上吧,.asm文件很簡單簡單的inlinhook就行了
#include <Ntifs.h>#include <ntimage.h>extern void debg();//關閉寫保護KIRQL WPOFFx64(){ KIRQL irql = KeRaiseIrqlToDpcLevel(); UINT64 cr0 = __readcr0(); cr0 &= 0xfffffffffffeffff; __writecr0(cr0); _disable(); return irql;}//開啟寫保護void WPONx64(KIRQL irql){ UINT64 cr0 = __readcr0(); cr0 |= 0x10000; _enable(); __writecr0(cr0); KeLowerIrql(irql);}//這里嘗試過tp的雙機調試,環境為win10 1903//----------------------------------------------------------------------------------------------------------------------------------------------------------------//1、首先解決The context is partially valid. Only x86 user-mode context is available. /*nt!KdpTrap:fffff807`64bfffc8 48895c2408 mov qword ptr [rsp+8],rbxfffff807`64bfffcd 4889542410 mov qword ptr [rsp+10h],rdxfffff807`64bfffd2 57 push rdifffff807`64bfffd3 4883ec40 sub rsp,40hfffff807`64bfffd7 33d2 xor edx,edx*/ULONG64 orgkdt = 0xfffff80166201fc8;//ULONG64 orgkdt= 0xfffff80764bfffc8;//直接寫硬編碼,這里需要進行修改<-------------------------------------------------------------------------------------------------------------------------------------------------------NTKERNELAPI UCHAR * PsGetProcessImageFileName(__in PEPROCESS Process);extern NTSTATUS hdbktrap(IN PKTRAP_FRAME TrapFrame,IN PKEXCEPTION_FRAME ExceptionFrame,IN PEXCEPTION_RECORD ExceptionRecord,IN PCONTEXT ContextRecord,IN KPROCESSOR_MODE PreviousMode,IN BOOLEAN SecondChanceException);//這里做一個跳轉VOID ModifyKdpTrap(PVOID myaddress,PVOID targetaddress) { KIRQL irql; ULONGLONG myfun; UCHAR jmp_code[] = "/x48/xB8/xFF/xFF/xFF/xFF/xFF/xFF/xFF/x00/xFF/xE0/x00/x00";//mov rax xxx,jmp rax myfun = (ULONGLONG)myaddress;//替換成自己的函數地址 RtlCopyMemory(jmp_code + 2, &myfun, 8); //debg(); irql = WPOFFx64(); RtlCopyMemory(targetaddress, jmp_code, 12); WPONx64(irql);}//這里完成hookNTSTATUS HookKdpTrap( IN PKTRAP_FRAME TrapFrame, IN PKEXCEPTION_FRAME ExceptionFrame, IN PEXCEPTION_RECORD ExceptionRecord, IN PCONTEXT ContextRecord, IN KPROCESSOR_MODE PreviousMode, IN BOOLEAN SecondChanceException){ PEPROCESS hp = PsGetCurrentProcess(); if (!_stricmp((char *)PsGetProcessImageFileName(hp), "TASLogin.exe")){ return STATUS_SUCCESS; } return hdbktrap(TrapFrame, ExceptionFrame, ExceptionRecord, ContextRecord, PreviousMode, SecondChanceException);}//這里做一個還原void UnHookKdpTrap() { KIRQL irql; UCHAR orignal_code[] = "/x48/x89/x5c/x24/x08/x48/x89/x54/x24/x10/x57/x48/x83/xec/x40";//mov rax xxx,jmp rax irql = WPOFFx64(); RtlCopyMemory(orgkdt, orignal_code, 15); WPONx64(irql);}//----------------------------------------------------------------------------------------------------------------------------------------------------------------//----------------------------------------------------------------------------------------------------------------------------------------------------------------//2、 防止安全組件加載失敗VOID DisableKdDebuggerEnabled() { SharedUserData->KdDebuggerEnabled = FALSE; //防止安全組件加載失敗}//----------------------------------------------------------------------------------------------------------------------------------------------------------------//----------------------------------------------------------------------------------------------------------------------------------------------------------------//3、TP會清零KdDebuggerEnabled,這里做一個每隔一秒的定時器//----------------------------------------------------------------------------------------------------------------------------------------------------------------//----------------------------------------------------------------------------------------------------------------------------------------------------------------//4、斷鏈隱藏 kdcom,防止kdcom內存被清空導致和windbg通訊不了/*0: kd> dt _eprocessnt!_EPROCESS +0x000 Pcb : _KPROCESS +0x2e0 ProcessLock : _EX_PUSH_LOCK +0x2e8 UniqueProcessId : Ptr64 Void +0x2f0 ActiveProcessLinks : _LIST_ENTRY*/PDRIVER_OBJECT pDriverObject = NULL;typedef struct _KLDR_DATA_TABLE_ENTRY { LIST_ENTRY InLoadOrderLinks; PVOID ExceptionTable; ULONG ExceptionTableSize; PVOID GpValue; ULONG UnKnow; PVOID DllBase; PVOID EntryPoint; ULONG SizeOfImage; UNICODE_STRING FullDllName; UNICODE_STRING BaseDllName; ULONG Flags; USHORT LoadCount; USHORT __Unused5; PVOID SectionPointer; ULONG CheckSum; PVOID LoadedImports; PVOID PatchInformation;} KLDR_DATA_TABLE_ENTRY, *PKLDR_DATA_TABLE_ENTRY;VOID HideDriver(){ PKLDR_DATA_TABLE_ENTRY entry = (PKLDR_DATA_TABLE_ENTRY)pDriverObject->DriverSection; PKLDR_DATA_TABLE_ENTRY firstentry; UNICODE_STRING uniDriverName; firstentry = entry; // 初始化要隱藏驅動的驅動名 RtlInitUnicodeString(&uniDriverName, L"kdcom.dll"); while ((PKLDR_DATA_TABLE_ENTRY)entry->InLoadOrderLinks.Flink != firstentry){ if (entry->FullDllName.Buffer != 0){ if (RtlCompareUnicodeString(&uniDriverName, &(entry->BaseDllName), FALSE) == 0){ //DbgPrint("隱藏驅動 %ws 成功!/n", entry->BaseDllName.Buffer); // 修改 Flink 和 Blink 指針, 以跳過我們要隱藏的驅動 *((ULONG*)entry->InLoadOrderLinks.Blink) = (ULONG)entry->InLoadOrderLinks.Flink; entry->InLoadOrderLinks.Flink->Blink = entry->InLoadOrderLinks.Blink; /* 使被隱藏驅動LIST_ENTRY結構體的Flink, Blink域指向自己 因為此節點本來在鏈表中, 那么它鄰接的節點驅動被卸載時, 系統會把此節點的Flink, Blink域指向它相鄰節點的下一個節點. 但是, 它此時已經脫離鏈表了, 如果現在它原本相鄰的節點驅動被 卸載了, 那么此節點的Flink, Blink域將有可能指向無用的地址, 而 造成隨機性的BSoD. */ entry->InLoadOrderLinks.Flink = (LIST_ENTRY*)&(entry->InLoadOrderLinks.Flink); entry->InLoadOrderLinks.Blink = (LIST_ENTRY*)&(entry->InLoadOrderLinks.Flink); break; } } // 鏈表往前走 entry = (PKLDR_DATA_TABLE_ENTRY)entry->InLoadOrderLinks.Flink; }}//----------------------------------------------------------------------------------------------------------------------------------------------------------------//----------------------------------------------------------------------------------------------------------------------------------------------------------------//5、處理TP藍屏/*fffff807`642d2210 48895c2420 mov qword ptr [rsp+20h],rbxfffff807`642d2215 4488442418 mov byte ptr [rsp+18h],r8bfffff807`642d221a 56 push rsifffff807`642d221b 57 push rdifffff807`642d221c 4154 push r12fffff807`642d221e 4155 push r13fffff807`642d2220 4157 push r15fffff807`642d2222 4883ec20 sub rsp,20h*/#define KdEnteredDebugger 0xfffff80165d061e0//#define KdEnteredDebugger 0xfffff80764704100//直接寫硬編碼,這里需要進行修改<-----------------------------------------------------------------------------------------------------------------------------------------------extern PMDL hookIoAllocateMdl(__drv_aliasesMem PVOID VirtualAddress, ULONG Length, BOOLEAN SecondaryBuffer, BOOLEAN ChargeQuota, PIRP Irp);ULONG64 IoAllocateM=0;//這里做一個跳轉VOID ModifyIoAllocateMdl(PVOID myaddress, PVOID targetaddress) { KIRQL irql; ULONGLONG myfun; UCHAR jmp_code[] = "/x48/xB8/xFF/xFF/xFF/xFF/xFF/xFF/xFF/x00/xFF/xE0/x00/x00";//mov rax xxx,jmp rax myfun = (ULONGLONG)myaddress;//替換成自己的函數地址 RtlCopyMemory(jmp_code + 2, &myfun, 8); //debg(); irql = WPOFFx64(); RtlCopyMemory(targetaddress, jmp_code, 12); WPONx64(irql);}PMDL newIoAllocateMdl(__drv_aliasesMem PVOID VirtualAddress, ULONG Length, BOOLEAN SecondaryBuffer, BOOLEAN ChargeQuota, PIRP Irp){ //debg(); if(VirtualAddress == KdEnteredDebugger){ //DbgPrint("[KdEnteredDebugger] address: %p/n", KdEnteredDebugger); VirtualAddress = (PUCHAR)KdEnteredDebugger + 0x30; //據暗中觀察,+0x30 的位置恒為0 } return hookIoAllocateMdl(VirtualAddress, Length, SecondaryBuffer, ChargeQuota, Irp);}//這里做一個還原void UnHookIoAllocateMdl() { KIRQL irql; UCHAR orignal_code[] = "/x48/x89/x5c/x24/x20/x44/x88/x44/x24/x18/x56/x57/x41/x54/x41/x55"; irql = WPOFFx64(); RtlCopyMemory(IoAllocateMdl, orignal_code, 15); WPONx64(irql);}//----------------------------------------------------------------------------------------------------------------------------------------------------------------VOID DriverUnload(PDRIVER_OBJECT DriverObject) { //還原之前的KdpTraphook UnHookKdpTrap(); //還原之前的IoAllocateMdl UnHookIoAllocateMdl(); //取消定時器 DbgPrint("See You !/n");}NTSTATUS DriverEntry(PDRIVER_OBJECT DriverObject, PUNICODE_STRING RegPath) { pDriverObject = DriverObject; DriverObject->DriverUnload = DriverUnload; //這里把這個函數進行了hook ModifyKdpTrap(HookKdpTrap, orgkdt); //防止安全組件加載失敗 DisableKdDebuggerEnabled(); //摘掉kdcom的eprocess HideDriver(); //干掉TP藍屏 IoAllocateM = (ULONG64)IoAllocateMdl;//得到函數的地址 ModifyIoAllocateMdl(newIoAllocateMdl, IoAllocateMdl); //設置定時器 return STATUS_SUCCESS;}
新聞熱點
疑難解答